Your Money, Reputation and Liability is on the Line.
The data breach at Capital One, one of the largest credit card issuers, affected over one hundred million people. One hundred million just in the U.S. There were an additional six million Canadian records also compromised in the breach.
The affected data came from general information given by customers during credit card applications. Types of data that were compromised consisted of names, addresses, ZIP and postal codes, phone numbers, email addresses, birth dates, self-reported income. 140,000 Social Security numbers and 80,000 linked bank accounts of secured credit card customers were also accessed, as well as approximately one million Social Insurance numbers of Canadian users.
Capital One has issued a statement that assured no credit card account numbers or log-in credentials were compromised, nor were 99 percent of Social Security numbers.
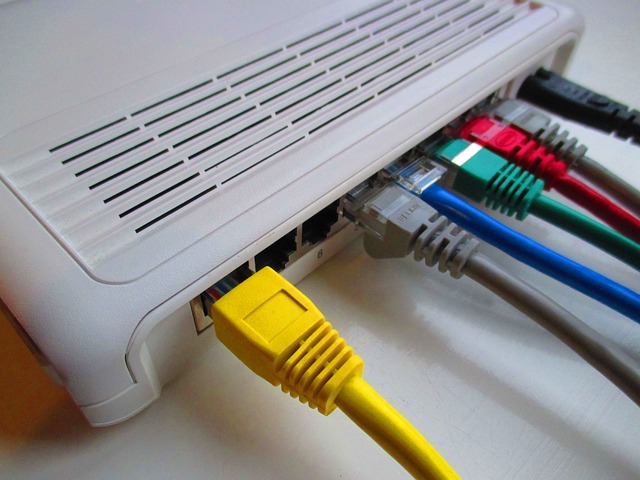
The alleged attacker, a former software engineer in Seattle and a former employee of Amazon Web Services (AWS) – where Capital One stored its information, was able to breach AWS S3 storage buckets and gain information through a misconfiguration error in a web application firewall (WAF), which let privileged commands be executed using Capital One credentials that had sufficient privileges to access the bank’s data.
Last week we learned that Equifax will pay up to $700 million in settlement costs associated with its 2017 massive data breach. Capital One faces the same possibility, in addition to other costs associated with this breach like restoring the bank’s reputation and repairing the breach.
Unfortunately, it’s not only large companies with millions of customers who face this type of attack. In a new study by IBM and the Ponemon Institute, we see that small and medium businesses are vulnerable too. An attack can be even more devastating for them because it’s much harder for small businesses, like many law firms, to be able to afford the consequences of a breach and stay afloat.
“The financial consequences of a data breach can be particularly acute for small and midsize businesses. In the study, companies with less than 500 employees suffered losses of more than $2.5 million on average — a potentially crippling amount for small businesses, which typically earn $50 million or less in annual revenue,” wrote IBM in its report.
How can we prevent this from happening to us?
This is the question many business owners, especially law firms, are asking after a breach like this.
For law firms of every size, cybersecurity will be a continuing challenge. You need to immediately formulate strategies and processes around data breach prevention, detection, and response. Because law firms often deal with highly sensitive information, it’s not surprising they have a target on their back when it comes to hacking. It’s a necessity for law firms to have full client trust, which means they have a duty to protect their clients’ sensitive information. Hackers are now bypassing bigger firms because small to medium-sized law firms are often the weaker link.
It’s time for your law firm to employ risk-reducing best practices to prevent what happened to Capital One happen to you. Here are 5 recommendations to start protecting your firm:
1. Guard Against Access to Resources
An apparent contributor to the breach was in an identity and access management (IAM) role that had excessive privileges. To combat this possibility, ensure your policies allow the fewest actions and access to resources as possible.
2. Implement and Practice an Incident Response Plan
Capital One avoided even more issues by acting quickly and transparently within their company as well as with customers and the public. Make sure your firm has an incident response plan including all sectors including legal, PR, etc. Practicing this plan will give you some degree of control and help alleviate a potentially disastrous situation.
3. 24/7 Monitoring
Constant monitoring can expose anomalous activity, which allows you to stop an attack in its tracks before it becomes a catastrophic breach. Cybercriminals can strike at any time, from anywhere in the world. You need to continuously monitor user and admin activity to look for suspicious authentication/login activity, policy or configuration changes, privilege escalations, etc.
4. Training Employees
Phishing attacks are by far the most frequent cyber-attack on small or local businesses and training your employees to know when a suspicious email is an attack could stop a crisis in its tracks. Creating a cyber-consciousness culture should top of mind for any law firm. Encourage a smarter, more secure workplace with our 5-Minute Guide to Cyber Security. Print it out or mount it somewhere in your office: https://jdlgrp.com/5-Minute-Guide-Cyber-Consciousness
5. Choose a Security Operations Center-as-a-Service
If you don’t have the resources or time to implement the above on your own, consider hiring an MSSP to protect your firm. SOC-as-a-service helps protect companies by combining machine learning and human expertise. The benefits include threats and vulnerabilities being analyzed in real-time and around the clock and evaluating and prioritizing risks. You also have access to a dedicated team of experts who function as your own security team. This will reduce your risk of being the next target for a breach, and you’ll gain the advantage of having the ability to respond to breaches in minutes instead of weeks.
For more information on a free dark web scan and how to keep your law firm safe from being breached, contact the JDL team at 973-607-2140 or fill out the form below.
SOURCES:
https://arcticwolf.com/blog/4-recent-breaches-highlight-the-need-for-soc-as-a-service-to-protect-sensitive-data/
https://www.darkreading.com/cloud/capital-one-what-we-should-learn-this-time/d/d-id/1335426
https://arcticwolf.com/blog/4-recent-breaches-highlight-the-need-for-soc-as-a-service-to-protect-sensitive-data/
https://arcticwolf.com/blog/the-capital-one-breach-its-impact-and-what-it-teaches-us-about-cybersecurity/
https://databreachcalculator.mybluemix.net/
https://jdlgrp.com/protecting-law-firm-2019-part-2/