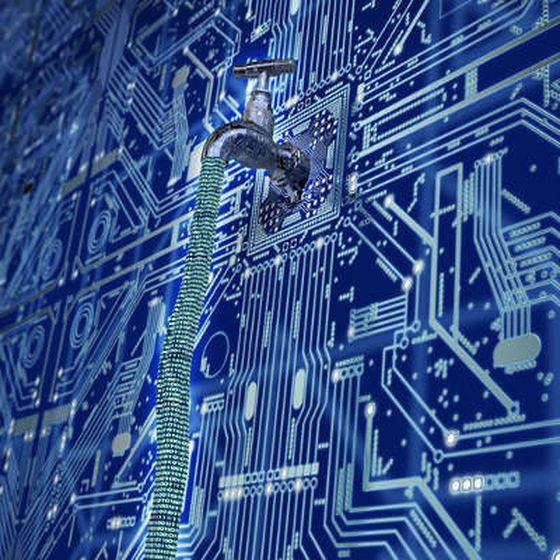
An insider threat is just what it sounds like. Any time an organization’s security is threatened from an employee or third party within, data and profitability are at risk. Vulnerability management helps analyze risk. Threats can be malicious when insiders intentionally cause leaks and data breaches to seek revenge or obtain money. Occasionally, hackers from a competing or opposing organization gain employment or act as a supplier for the purpose of carrying out an insider attack.
Often threats occur because employees accidentally delete important data, participate in a phishing effort or thoughtlessly share more data than they should with an outside source. Employees might accidentally send data that should be kept secure to the wrong email address or share files they don’t realize contain confidential information.
Dangers of Insider Threats
Insider threats are some of the most expensive and pervasive security risks facing businesses of all sizes. Consider the following statistics:
- More than half of companies that experienced an insider attack said they spent at least $100,000 to fix the breach.
- For 12 percent of the organizations attacked, remediation costs were in excess of $1 million.
- Seventy-four percent of companies surveyed in the 2017 Insider Threat Report said they felt vulnerable to insider threats.
Some industries are attacked more often than others. Medical facilities spend large sums preventing health care data breaches and law firms focus on legal security and compliance because of the high cost associated with remediating compromised data.
Insider threats are devastating because they often go undetected, sometimes for years. When employees must regularly access sensitive information and systems, it’s hard to tell if they’re just doing their job or providing information to unauthorized parties. The longer it takes for an organization to notice a breach, the more data is unsecure.
Malicious behavior is even harder to prove. Well-trained hackers know how to cover their tracks, and innocent employees may not even know what they did wrong. In both cases, it can be impossible to prove guilt or isolate who is responsible.
Most Common Causes and How to Prevent Them
While anyone who has access to data can be an insider threat, organizations should focus most on these groups:
 Users with high levels of clearance. Administrators, department heads and IT specialists typically have the highest access to sensitive data. Even the most trustworthy and committed staff can make errors that create a breach. Provide a clear understanding of system connection protocols even for leadership. Specify safe activities and what behaviors create risk.
Users with high levels of clearance. Administrators, department heads and IT specialists typically have the highest access to sensitive data. Even the most trustworthy and committed staff can make errors that create a breach. Provide a clear understanding of system connection protocols even for leadership. Specify safe activities and what behaviors create risk.- Outside parties with access. Employees who work outside of your facility, suppliers and subcontractors often receive permission to access data to do their job, but they can pose a threat to data security. Protect users from accidentally causing a problem with network segregation. Experts can set systems to check for unauthorized activity, partition suspicious files off from the network and prevent third parties from accessing files they shouldn’t.
- Disgruntled or previous employees. When you ask an employee to leave, make sure they don’t take data with them. USB, smart phones, and email transfers are simple ways to transfer data off premise. Know which data are sensitive and what employees can access before their termination. Make a practice of giving people the least amount of access they need to minimize the risk, and review user activity to check for misuse. Disable access immediately upon resignation or termination.
Contact Us
JDL Group can help you implement the right strategy to protect your organization from insider threats. Contact us today.
Additional Resources:
https://www.scmagazineuk.com/the-insider-threat-the-biggest-threat-in-banking-cyber-security/article/654525/
https://blog.netwrix.com/2017/12/07/7-tips-to-avoid-data-theft-by-ex-employees/
https://www.welivesecurity.com/2017/05/26/3-types-employees-cause-data-breach/
https://www.tripwire.com/state-of-security/security-data-protection/insider-threats-main-security-threat-2017/